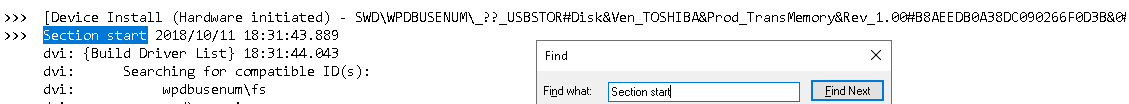
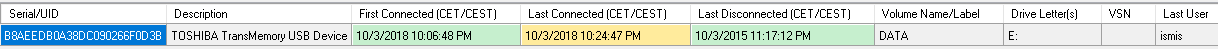
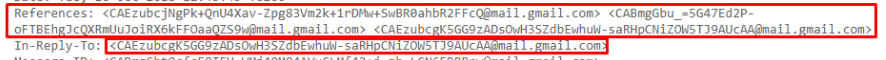
윈도우에 장착되었던 부품들(cpu, 메인보드, 램 등)에 대해 확인하려면
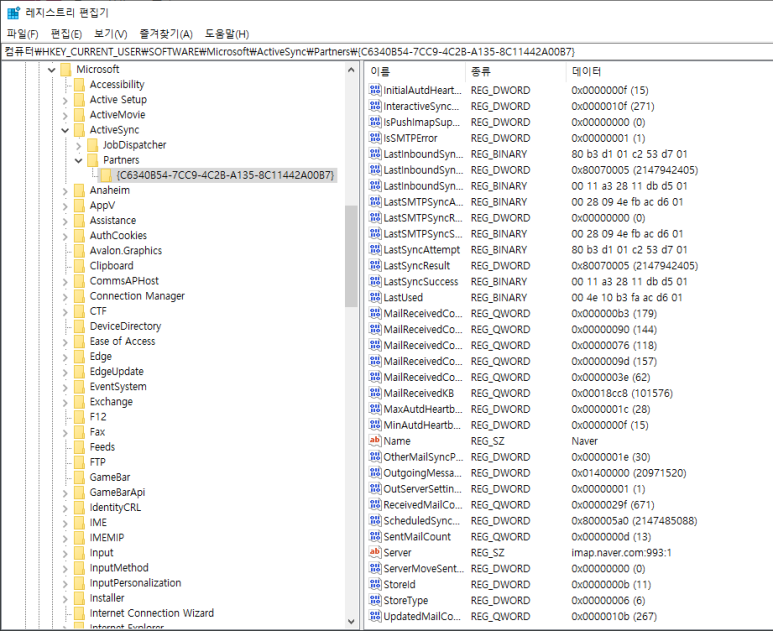
레지스트리를 봐야함
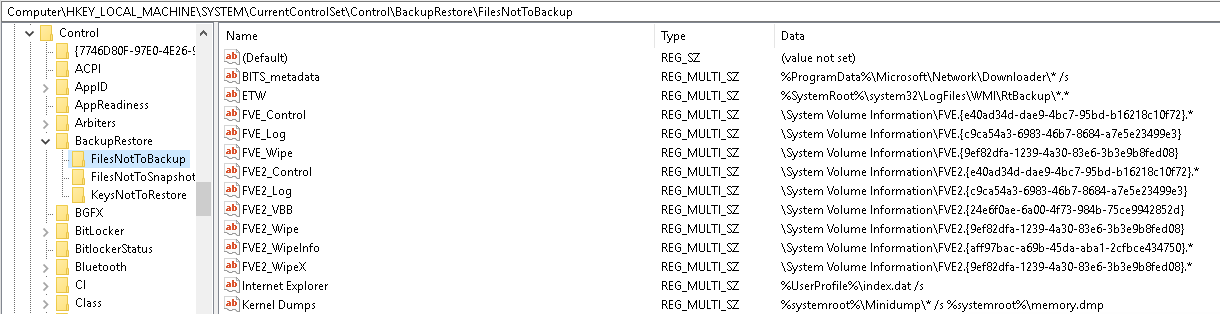
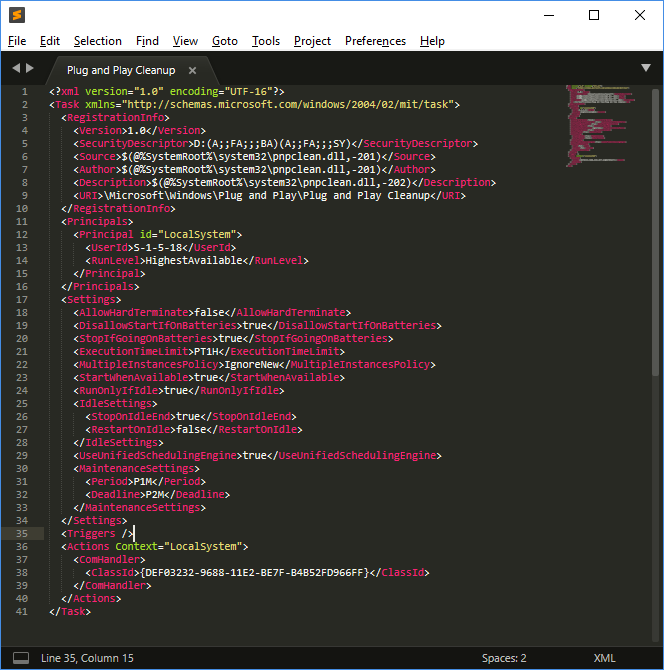
레지스트리의 다음 트리는 드라이버 작성기( HKLM 이 HKEY_LOCAL_MACHINE 나타내는 위치)에 특히 관심이 있습니다.
HKLM\SYSTEM\CurrentControlSet\Services 레지스트리 트리
HKLM\SYSTEM\CurrentControlSet\Control Registry Tree
HKLM\SYSTEM\CurrentControlSet\Enum 레지스트리 트리
HKLM\SYSTEM\CurrentControlSet\HardwareProfiles 레지스트리 트리
WDF(KMDF 또는 UMDF) 드라이버에서 레지스트리 키에 액세스하는 방법에 대한 자세한 내용은 드라이버용 레지스트리 키 소개를 참조하세요.
WDM 드라이버에서 레지스트리 키에 액세스하는 방법에 대한 자세한 내용은 플러그 앤 플레이 레지스트리 루틴을 참조하세요.
--------------------------------------------------
HKLM\SYSTEM\CurrentControlSet\Services 레지스트리 트리는 시스템의 각 서비스에 대한 정보를 저장합니다. 각 드라이버에는 HKLM\SYSTEM\CurrentControlSet\Services\DriverName 형식의 키가 있습니다. PnP 관리자는 드라이버의 DriverEntry 루틴을 호출할 때 RegistryPath 매개 변수에서 드라이버의 이 경로를 전달합니다.
HKLM\SYSTEM\CurrentControlSet\Control 레지스트리 트리에는 시스템 시작 및 디바이스 구성의 일부 측면을 제어하기 위한 정보가 포함되어 있습니다. 다음 하위 키는 특히 관심이 있습니다.
HKLM\SYSTEM\CurrentControlSet\Enum 열거형 트리는 운영 체제 구성 요소에서 사용하도록 예약되어 있으며 레이아웃은 변경될 수 있습니다. 드라이버 및 사용자 모드 디바이스 설치 구성 요소는 IoGetDeviceProperty, CM_Get_DevNode_Registry_Property 및 SetupDiGetDeviceRegistryProperty 와 같은 시스템 제공 함수를 사용하여 이 트리에서 정보를 추출해야 합니다.
HKLM\SYSTEM\CurrentControlSet\HardwareProfiles 레지스트리 트리에는 시스템의 하드웨어 프로필에 대한 정보가 포함되어 있습니다. 하드웨어 프로필은 더 이상 사용되지 않으며 하드웨어 프로필을 기준으로 상태를 저장해서는 안 됩니다.
'포렌식 > 컴퓨터' 카테고리의 다른 글
| MessageAnalyzer(이벤트 로그 분석 프로그램) (0) | 2023.05.16 |
|---|---|
| Study on Windows Event Log-Based Corporate Security Audit and Malware Detection (0) | 2023.05.15 |
| encase에서 비트락커 메시지 다시 띄우기 (0) | 2023.02.14 |
| 윈도우 10 이벤트 로그 중 연결 장치(저장장치) 흔적 확인 (0) | 2022.11.16 |
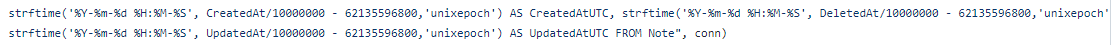
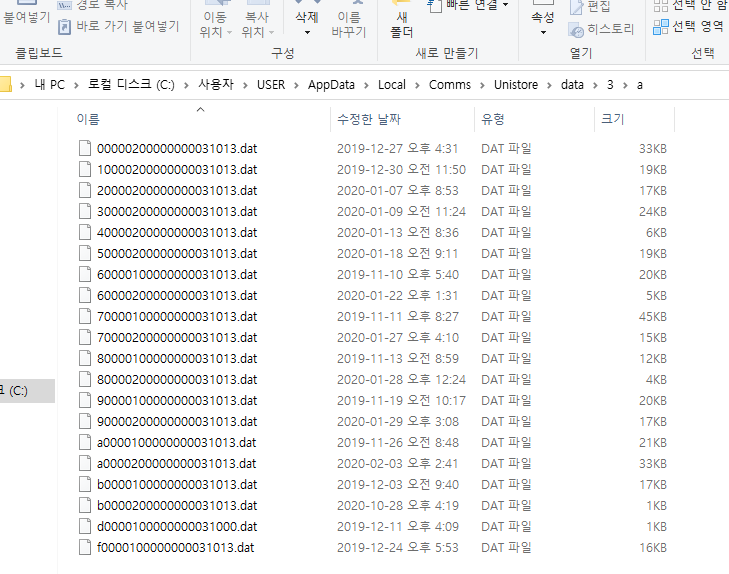
| sticky 메모(스티키 메모) db에서 시간 데이터 변환 쿼리문 (0) | 2022.09.26 |